Learn Why CloudExtend Adheres to NetSuite’s Role-Based Access Control
If you have invested in Oracle NetSuite, you have already made a strong commitment to keeping your crucial business data in a highly secure, standards-compliant cloud environment even when using third-party applications. Being the guardian for sensitive data of over 22,000 companies worldwide is a massive responsibility: NetSuite takes security very seriously.
Your NetSuite account’s security is vulnerable at its weakest link: people.
While NetSuite has stringent guards against unauthorized access to your account, it has to trust those that you’ve chosen to let in. This is where Role-Based Access Control (RBAC) becomes a key factor. With RBAC, NetSuite admins can decide which users have access to view, add, remove, or modify data in the account. NetSuite even bundles in a number of common pre-configured roles, allowing admins to apply these controls with little effort.
However, NetSuite is not just an application that users interact with through a browser. It’s a rich ecosystem with thousands of integration applications built by third parties. This is obviously a wonderful fact about NetSuite. If a feature is not natively available from NetSuite, you probably can find it on SuiteApp.com
Alternatively, you can also create something yourself using Celigo’s visionary integrator.io platform.
If not careful, you may introduce another weak link to your account’s security: third party apps.
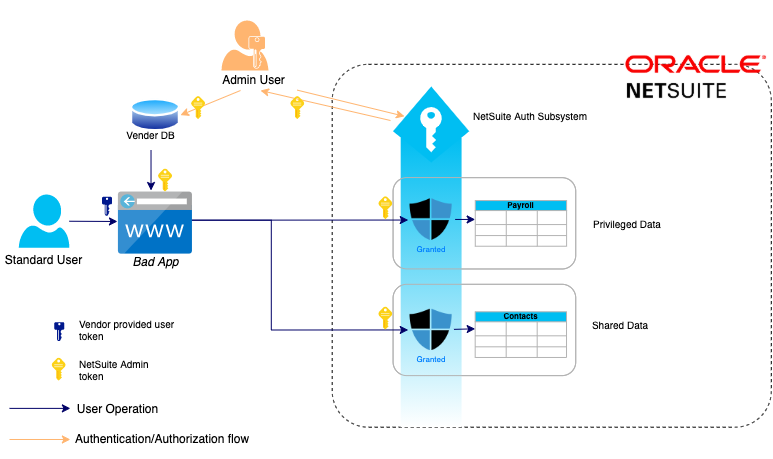
For instance, we’ve seen applications that process all user operations on NetSuite data, with a single token generated by a NetSuite admin user. This is a common pattern adopted by system-to-system, background data integration applications.
Some user-interactive applications tend to follow the same pattern which effectively bypasses NetSuite RBAC by distributing a single token with admin access to all the users of the application. In its place, these applications would have some custom authorization logic that falls far short.
This is a dangerous approach borderlining on Security Architecture Anti-patterns such as “Browse-up” and “Management bypass” (source: National Cyber Security Center, UK). By using such an application with your account, you may circumvent the robust security apparatus that NetSuite has put in place for you.
CloudExtend products adhere strictly to NetSuite’s RBAC for user-interactive features.
Regardless of the powerful capabilities of the application, users are still bound by the security confines enforced by the NetSuite administrator. If the admin has blocked a user from accessing a certain record type in the NetSuite UI, he or she would see the same restrictions enforced in the CloudExtend app. There are no backchannels to exploit and elevate user access in this design.
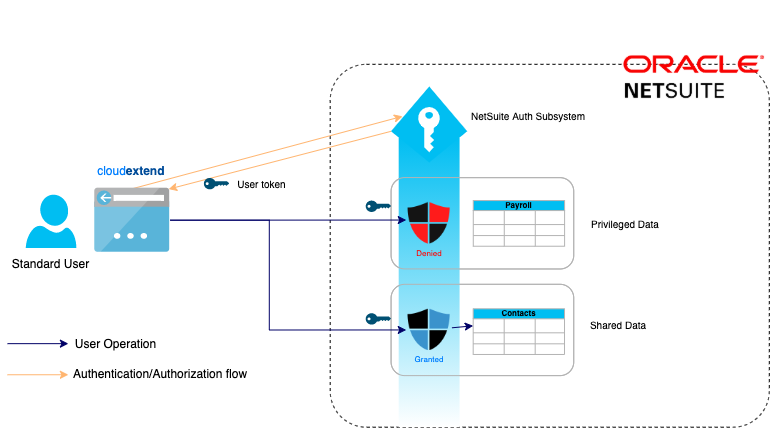
Apart from adhering to RBAC, with the support for NetSuite’s token-based Three-Step Authorization (3SA) feature, CloudExtend apps support multi-factor authentication (MFA) and single sign-on (SSO). It is compatible with any SAML SSO based Identity Provider including Azure Active Directory, Google, and Okta.
Recommendations
While we highly recommend 3SA to all our customers, we still support logging in via NetSuite’s basic credentials for those who have faced challenges adopting token-based authentication. As an administrator, if you are concerned about users using their credentials, you have the option of blocking such logins to specific applications or to any application through NetSuite permissions.
Applications that proxy user actions through an admin user token also prevent you from performing effective access control audits on your NetSuite account. When financial and other critical business information is at stake, accountability and visibility of user actions would be of paramount importance.
The Security of Your NetSuite Data is a Shared Responsibility
These are some of the advantages of using CloudExtend applications that adhere to the best practices enforced by the ecosystem. Ultimately, the security of your NetSuite data is a shared responsibility between NetSuite, you, and your users, and of course the solution providers you choose to work with. Be sure to evaluate your options based on the ethical and technical prowess of the vendors, not just the feature sets they advertise.
